The average large enterprise operates dozens of core systems. ERP platforms that run finance and operations. CRM systems that manage customer relationships. Supply chain applications that track inventory and logistics. HR systems that handle payroll and talent management. Industry-specific platforms that power core business functions.
None of these systems was meant to work together. Yet the business depends on them working together.
This is where APIs come in. They are the connective tissue of modern enterprise IT. They allow systems to exchange data, trigger processes, and coordinate activities. When APIs work well, they are invisible. Business processes flow smoothly. Data stays consistent. Operations run efficiently.
When APIs fail or, worse, when they are compromised, the impact is immediate and severe. Transactions halt. Data integrity breaks. Security breaches expose sensitive information. Business continuity suffers.
For C-level executives overseeing enterprise software delivery or large-scale digital transformation, API security is not a technical detail. It is a business risk that determines whether your integration strategy succeeds or becomes a liability.
Why API Security Matters More Than Ever
Ten years ago, most enterprise integrations happened through batch processes. Files were moved between systems overnight. Point-to-point connections linked specific applications. Integration was slow but contained. A failure in one integration rarely cascaded to others.
Today’s enterprises operate differently. APIs enable real-time integrations. Customer-facing applications call backend systems instantly. Partner platforms exchange data continuously. Mobile apps access enterprise services on demand. Cloud migrations create hybrid environments where on-premise and cloud systems must communicate seamlessly.
This real-time, always-connected model creates enormous business value. It also creates enormous risk.
APIs expose your systems to the outside world. Every API endpoint is a potential entry point for unauthorized access. Unlike traditional systems protected by firewalls and VPNs, APIs are designed to be accessible, often from the internet, sometimes to third parties, always from multiple sources.
Integration failures cascade quickly. In a batch integration model, a failure is contained until the next scheduled run. In real-time API integrations, a failure propagates instantly. A compromised API can spread malicious activity across connected systems before anyone notices.
Legacy systems were not designed for API security. Many enterprises expose decades-old core systems through APIs. These legacy platforms lack modern security controls. They were built in an era when security meant perimeter defence, not granular access control and continuous monitoring.
Third-party dependencies multiply risk. Modern enterprises integrate with numerous external partners, payment processors, logistics providers, data aggregators, and cloud services. Each partner connection is an API relationship. Each API relationship is a trust boundary that must be secured and monitored.
Regulatory scrutiny is increasing. Data protection laws require enterprises to secure personal information wherever it flows. APIs that move customer data, financial records, or health information must meet strict security standards. Regulators increasingly ask: how do you secure your APIs? How do you monitor data flows? How do you control access?
What Actually Goes Wrong in Enterprise API Programs
Large enterprises struggle with API security for reasons that have little to do with technology and everything to do with execution.
API security is an afterthought. In many integration programs, the focus is on making systems talk to each other. Does the data flow? Does the integration work? Security reviews happen later, often just before go-live, when fixing issues means delays and cost overruns.
Governance is unclear. Who owns API security? Is the team building the API? Is the team consuming it? The enterprise architecture group? The information security team? When accountability is diffused, standards vary. Some APIs have strong authentication. Others use weak credentials. Some log all access. Others have no audit trail.
Documentation is poor or non-existent. Developers build APIs to solve immediate integration needs. Documentation is minimal “Here’s the endpoint, here’s the payload format.” Security requirements, rate limits, error handling, and authentication flows are discovered through trial and error or by reading code.
Legacy authentication patterns persist. Many enterprise APIs still use basic authentication with usernames and passwords, sometimes hardcoded in configuration files or passed in plain text. Modern patterns, such as OAuth, API keys with rotation policies, and mutual TLS, are discussed but not implemented, especially for internal integrations where security is assumed rather than enforced.
API proliferation creates blind spots. Enterprises often have no central inventory of their APIs. Teams build integrations as needed. Shadow IT creates unofficial APIs. Acquisitions bring APIs from acquired companies. No one knows the full API landscape. You cannot secure what you cannot see.
Rate limiting and throttling are missing. Without proper controls, a single badly behaving consumer can overwhelm an API, causing service degradation or outages. Malicious actors can use unthrottled APIs to exfiltrate large volumes of data or mount denial-of-service attacks.
Monitoring is reactive, not proactive. Most enterprises only monitor API performance—response times, error rates, and availability. Security monitoring is limited. Unusual access patterns, failed authentication attempts, and anomalous data volumes these signals exist but are not tracked or acted upon.
Testing focuses on functionality, not security. Integration testing validates that data flows correctly. Load testing ensures the API can handle volume. But security testing, penetration tests, vulnerability scans, and authentication bypass attempts often get deferred or skipped entirely.
The Hidden Costs of Insecure APIs
When API security fails, the costs extend far beyond the immediate breach.
Data breaches through APIs make headlines. Some of the largest data breaches in recent years happened through insecure APIs. Attackers discovered endpoints with weak authentication or excessive data exposure and extracted millions of customer records. The financial penalties, legal costs, and reputation damage are measured in millions, sometimes billions.
Integration outages disrupt business operations. A compromised API can be taken offline immediately, breaking integrations and halting dependent business processes. If your e-commerce platform relies on an inventory API that gets compromised, you cannot process orders until the API is secured and restored.
Remediation diverts resources from strategic initiatives. When API security issues are discovered late, fixing them consumes enormous time and effort. Development teams stop new feature work. Security teams conduct emergency audits. Leadership focuses on damage control instead of strategy.
Compliance violations trigger regulatory action. APIs that expose personal data without proper security controls violate privacy regulations. Regulators impose fines. They mandate remediation plans. They increase oversight. The compliance burden grows.
Trust with partners erodes. If your APIs are the integration point with business partners, a security incident damages those relationships. Partners question your security maturity. They impose additional requirements. Some may terminate relationships entirely.
What Separates Secure API Programs from Insecure Ones
Enterprises that manage API security well across large-scale integrations share certain characteristics. They do not necessarily have the most advanced technology. They have disciplined execution and clear governance.
API security is designed in, not bolted on. In well-run programs, security requirements are defined before the first API is designed. Authentication mechanisms are chosen. Authorization models are established. Logging and monitoring standards are set. Every API built follows these standards from the beginning.
Ownership and accountability are explicit. Successful enterprises assign clear ownership for API security. API producers are responsible for implementing security controls. API consumers are responsible for using credentials securely. A central API governance team sets standards, reviews designs, and monitors compliance. When something goes wrong, accountability is clear.
APIs are treated as products, not projects. APIs have lifecycles. They need versioning strategies, deprecation plans, and ongoing support. Treating APIs as products means investing in documentation, developer experience, and long-term maintenance. It means monitoring usage, gathering feedback, and continuously improving security posture.
Standards are enforced, not suggested. Leading enterprises establish API security standards and enforce them through automated checks. APIs cannot be deployed to production without passing security scans. Authentication methods outside the approved list are rejected. Non-compliant APIs are flagged and remediated.
Visibility is comprehensive. Mature enterprises maintain API catalogues that document every API, its purpose, its security controls, and its consumers. They monitor API traffic in real-time. They detect anomalies and respond quickly. They know their API landscape and can secure it effectively.
Partners are held to the same standards. When integrating with external vendors or partners, enterprises that excel do not assume third-party APIs are secure. They conduct security assessments. They review authentication methods. They monitor third-party API behaviour. Security expectations are written into contracts and validated regularly.
The Role of Leadership in API Security
API security is often perceived as a technical problem to be solved by developers or security engineers. In reality, it is a governance problem that requires executive attention.
When a CIO or CTO signals that API security is a priority through resource allocation, governance structures, and accountability frameworks, the organization responds.
This means asking the right questions in governance forums.
Not just “how many APIs do we have?” but “do we have a complete inventory of our APIs and their security postures?”
Not just “are our APIs documented?” but “do our APIs meet enterprise security standards, and how do we verify compliance?”
Not just “did the integration work?” but “did we validate that the integration is secure before connecting production systems?”
Leadership also means making investment decisions. API security requires tooling, API gateways, identity management platforms, and security monitoring systems. These are not free. They require budget, implementation effort, and ongoing operation. Leaders who understand that API security is foundational to integration strategy make these investments without waiting for an incident to justify them.
Building Secure APIs from the Ground Up
For enterprises embarking on integration programs or modernizing existing API landscapes, how do you build security in from the start?
Establish API security standards early. Before teams start building APIs, define what secure means. Which authentication methods are approved? OAuth with tokens? API keys with rotation? Mutual TLS for high-security scenarios? What authorization model will you use—role-based access control, attribute-based, or something else? How will you handle secrets and credentials? Document these standards clearly and train teams on them.
Choose authentication carefully. Not all authentication methods are equal. Basic authentication with username and password is simple but risky, especially if credentials are stored insecurely or transmitted without encryption. Token-based authentication with OAuth provides better security, especially when tokens have limited scope and short lifetimes. For the highest-security scenarios, financial transactions, health data,and system-to-system integrations mutual TLS ensures both parties authenticate each other.
Implement authorization at the API level. Authentication answers “who are you?” Authorization answers “what are you allowed to do?” Many APIs authenticate users but fail to enforce granular permissions. Every API endpoint should check not just whether the caller is authenticated, but whether they are authorized for the specific action and data they are requesting.
Design for least privilege. API consumers should have access only to the data and operations they need, nothing more. If a mobile app needs to read customer profiles, it should not have permission to delete accounts. If a reporting system needs sales data, it should not have access to payment card information. Scope API permissions tightly and review them regularly.
Validate all inputs. APIs are attack surfaces. Malicious actors can send unexpected or malformed data, hoping to exploit vulnerabilities. Every API should validate inputs, check data types, enforce length limits, sanitize special characters, and reject unexpected fields. Input validation prevents injection attacks and data corruption.
Encrypt data in transit. All API traffic should use HTTPS with modern TLS versions. This is not optional for public-facing APIs and should not be skipped for internal APIs. Network sniffing, man-in-the-middle attacks, and credential theft are real risks even within enterprise networks.
Implement rate limiting and throttling. Protect APIs from abuse by limiting how many requests a consumer can make in a given time period. Rate limits prevent denial-of-service attacks, accidental resource exhaustion, and large-scale data exfiltration. Different consumers may have different limits based on their needs and trust level.
Log everything relevant. Comprehensive logging is essential for security monitoring and incident response. Log who called the API, when, what they requested, whether authentication succeeded, what data was accessed, and whether errors occurred. Logs should be tamper-proof, stored securely, and retained for the period required by compliance obligations.
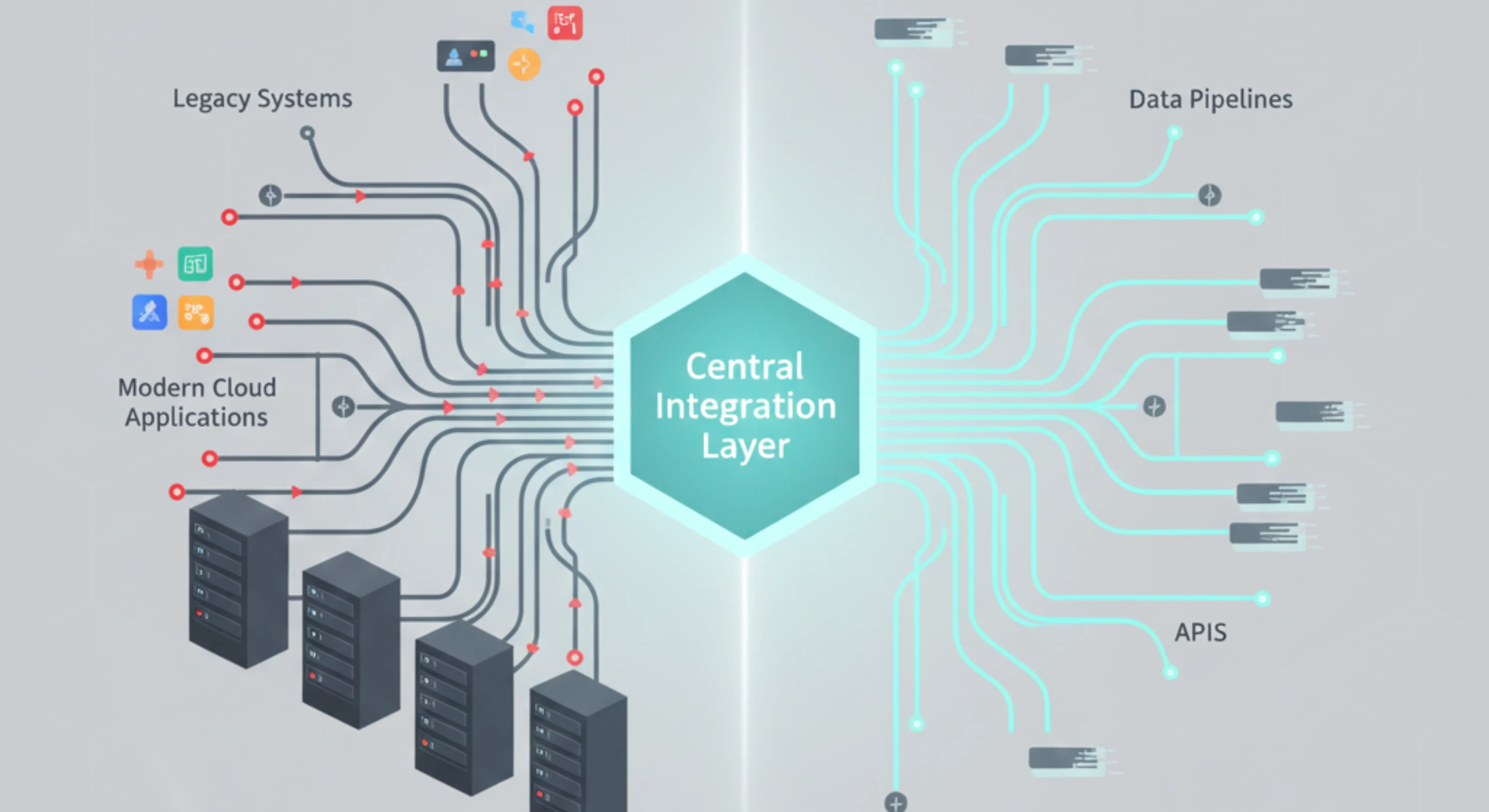
Use API gateways for centralized control. Rather than implementing security controls in every API individually, use an API gateway as a centralized enforcement point. Gateways handle authentication, authorization, rate limiting, logging, and monitoring consistently. They provide visibility across all APIs and simplify governance.
Version APIs properly. As APIs evolve, security requirements change. New versions may use different authentication methods, expose different data, or have different access controls. Maintain clear versioning. Support older versions only as long as necessary. Communicate deprecation timelines clearly to consumers.
Document security requirements. Good API documentation includes more than just endpoint definitions and payload formats. It explains authentication flows, authorization requirements, rate limits, error codes, and security best practices for consumers. Documentation helps consumers use APIs securely.
Securing Legacy System Integrations
One of the hardest challenges in enterprise API security is exposing legacy systems that were never designed with APIs in mind.
These systems are often core to business operations and lack modern security controls. They may use fixed passwords, lack audit logging, or have no concept of granular permissions. Yet they hold critical data that must be accessible to modern applications.
Do not expose legacy systems directly. Building APIs that directly front legacy systems is risky. Instead, use an integration layer or API gateway that sits between the legacy system and consumers. This layer enforces modern security controls, translates authentication methods, adds logging and monitoring, and provides a point of defence.
Transform authentication at the boundary. Legacy systems may require basic authentication, but that does not mean your APIs should. The integration layer can accept modern authentication OAuth tokens or API keys and translate them to the credentials the legacy system expects. Credentials for the legacy system are stored securely and never exposed to consumers.
Restrict access to integration services. If your integration layer is the only path to the legacy system, enforce that restriction at the network level. Legacy systems should not be directly accessible from the broader network. This limits the attack surface and forces all access through the secured integration layer.
Add audit logging where none exists. Even if the legacy system does not log access, your integration layer can. Log every request, every query, every data extraction. This creates visibility that did not exist before and supports compliance and incident investigation.
Monitor for anomalies. Legacy systems often have predictable access patterns. The integration layer can baseline normal behaviour, typical request volumes, expected data sizes, and standard query patterns. Deviations from normal trigger alerts might indicate compromise or misuse.
Managing Third-Party API Risks
Enterprise integrations extend beyond internal systems to include third-party APIs, payment gateways, logistics platforms, marketing services, data providers, and cloud platforms.
Each third-party integration is a trust relationship. You are sending data to systems you do not control, relying on security you do not implement.
Conduct security assessments before integration. Do not assume third-party APIs are secure. Review their security documentation. Ask about authentication methods, encryption standards, data retention policies, and incident response procedures. For high-risk integrations, request security certifications or audit reports.
Use secure credential management. Third-party APIs typically require credentials, API keys, tokens, and client secrets. These must be stored securely, never hardcoded in source code or configuration files. Use secret management tools or vaults. Rotate credentials regularly. Revoke credentials when integrations are decommissioned.
Limit data sharing. Send third-party APIs only the data they need to perform their function. If a payment processor needs transaction amounts and account identifiers, do not send full customer profiles. Minimizing data exposure reduces risk if the third party is compromised.
Monitor third-party API behaviour. Track response times, error rates, and data volumes from third-party APIs. Unusual patterns, sudden spikes in errors, slow responses, and unexpected data sizes may indicate problems with the third-party service. Early detection allows you to respond before impact spreads.
Have contingency plans. If a third-party API fails or is compromised, what is your fallback? Can you switch to an alternative provider? Can you operate without the integration temporarily? Contingency planning should be part of every third-party integration strategy.
Review contracts for security obligations. Third-party API contracts should specify security responsibilities. What happens in a breach? How quickly must they notify you? What are their obligations for data protection? Can you audit their security controls? Clear contractual terms protect your enterprise if things go wrong.
Choosing Partners for API-Driven Integration Programs
Most large enterprises rely on external partners to design, build, and operate complex integration landscapes. The partner you choose significantly influences your API security posture.
When evaluating potential partners for enterprise program management or IT transformation strategy, API security capabilities should be a primary consideration.
What is their approach to API security? Ask about their API design standards, authentication methods, and security testing practices. Look for evidence of security-first design, not security as an afterthought. Partners who have delivered secure API integrations for regulated industries bring valuable experience.
How do they handle credentials and secrets? Partners working on your integration programs will need access to credentials, API keys, and certificates. How do they manage these securely? Do they use secret management tools? Do they rotate credentials? Do they revoke access when team members leave?
What is their testing methodology? Beyond functional testing, do they conduct security testing? Penetration tests? Vulnerability scans? Authentication bypass attempts? API security testing should be routine, not exceptional.
How do they ensure compliance? If your integrations involve regulated data, financial records, health information, or personal data, your partner must understand compliance requirements. They should know how to design APIs that meet regulatory standards and how to document compliance evidence.
Do they provide operational support? API security does not end at deployment. Ongoing monitoring, incident response, and continuous improvement are essential. Partners who offer operational support like Ozrit, which works with enterprises on large-scale digital transformation, understand that API security is a long-term responsibility, not a project deliverable.
Monitoring and Incident Response for API Security
Even with the best design and implementation, API security requires continuous monitoring and rapid incident response.
Implement comprehensive API monitoring. Track not just performance metrics, but security metrics. Who is calling your APIs? Are authentication rates normal? Are there unusual spikes in failed requests? Are data volumes consistent with expectations? Security monitoring provides early warning of potential compromises.
Use anomaly detection. Establish baselines for normal API behaviour. Then detect deviations—a normally low-volume API suddenly receiving thousands of requests, a consumer who typically accesses one dataset now accessing many, and authentication failures from unusual locations. Anomalies may indicate attacks, misconfigurations, or compromised credentials.
Alert on security events. Configure alerts for critical security events, repeated authentication failures, access to sensitive endpoints, rate limit violations, and unusual data exports. Alerts should trigger immediate investigation, not sit unnoticed in logs.
Have an incident response plan specific to APIs. When an API is compromised, what are the steps? Who is notified? How do you isolate the affected API? How do you revoke compromised credentials? How do you assess what data was exposed? An API-specific incident response plan ensures quick, coordinated action.
Conduct post-incident reviews. After an API security incident, even a near-miss, conduct a thorough review. What happened? Why was it not detected earlier? What controls failed? What improvements are needed? Post-incident learning strengthens future security.
Test incident response regularly. Do not wait for a real incident to discover gaps in your response plan. Conduct tabletop exercises that simulate API compromises. Walk through detection, containment, notification, and recovery. Refine the plan based on what you learn.
Building Institutional API Security Capability
One-time API security is not enough. Enterprises need institutional capability, the ability to design, build, and operate secure APIs consistently across programs, teams, and time.
Establish an API centre of excellence. Centralize API expertise, people who understand API design patterns, security best practices, and enterprise standards. This team sets standards, reviews designs, provides guidance, and maintains API governance. They ensure consistency and quality across all APIs.
Create reusable API templates and patterns. Rather than every team designing APIs from scratch, provide templates that embody security best practices. Authentication patterns, authorization frameworks, logging configurations, and error handling should be standardized and reusable. Templates accelerate delivery while ensuring security.
Invest in API management platforms. Modern API management platforms provide gateways, developer portals, analytics, and governance tools. They make it easier to enforce security policies, monitor usage, and manage API lifecycles. The right platform reduces manual effort and improves security posture.
Train developers on secure API design. Security is everyone’s responsibility, but not everyone has security training. Provide developers with education on common API vulnerabilities, secure coding practices, and enterprise standards. Make security training part of onboarding and ongoing professional development.
Measure and improve continuously. Track API security metrics, percentage of APIs meeting security standards, time to remediate vulnerabilities, authentication failure rates, and security incidents. Use these metrics to identify weaknesses and drive improvement. What gets measured gets managed.
The Long-Term View on API Security
APIs are not temporary integrations. They become foundational infrastructure. Systems depend on them. Business processes rely on them. They outlast projects, programs, and sometimes the teams that built them.
Securing APIs for the long term requires thinking beyond initial delivery.
Plan for credential rotation. Credentials used to access APIs should not be permanent. API keys, certificates, and tokens all should have expiration dates and rotation schedules. Long-lived credentials increase risk. Regular rotation limits exposure if credentials are compromised.
Maintain documentation over time. As APIs evolve, documentation must evolve. Security requirements change. New endpoints are added. Authentication methods are updated. Keeping documentation current ensures that future teams understand how APIs work and how to use them securely.
Monitor for emerging threats. The threat landscape evolves. Vulnerabilities are discovered in authentication protocols, encryption algorithms, and platforms. Stay informed about emerging threats relevant to your API landscape. Assess impact. Update controls as needed.
Plan for deprecation and replacement. APIs should not live forever. As systems evolve, old APIs should be deprecated and replaced. Plan deprecation timelines. Notify consumers well in advance. Provide migration paths. Shut down old APIs completely rather than leaving them as forgotten, unsecured endpoints.
Conduct regular security reviews. Even APIs that were secure when built can drift over time. Configuration changes, new integrations, and updated libraries can all introduce vulnerabilities. Regular security reviews ensure APIs remain secure throughout their lifecycle.
Final Thoughts
Secure API design for large enterprise integrations is not a purely technical challenge. It is an execution challenge that requires governance, discipline, and long-term commitment.
The technology for securing APIs exists. Modern authentication protocols, API gateways, and monitoring platforms are mature and accessible.
What separates enterprises that succeed from those that struggle is not access to technology. It is the discipline to design security in from the start, the governance to enforce standards consistently, and the maturity to treat API security as an ongoing responsibility rather than a one-time task.
For C-level executives overseeing enterprise software delivery or managing complex IT programs, API security is a strategic imperative. It determines whether your integration strategy enables business agility or creates business risk.
The cost of insecure APIs is high data breaches, compliance violations, operational disruptions, and reputation damage.
The benefit of secure APIs is equally high trusted integrations, regulatory confidence, business continuity, and sustainable growth.
Because in enterprise integration programs, APIs are not just technical interfaces. They are trust boundaries, data pathways, and business enablers. Securing them properly is not optional.
It is foundational to enterprise execution.